
Obidiegwu Onyedikachi Henry
Cloud Security Engineer

Cloud Security Engineer
I'm a Cloud Security Engineer with focus on secure cloud design, automated defense, and intelligent threat response across AWS, Azure, and hybrid environments. I merge DevSecOps principles, Zero Trust frameworks, and AI-driven security analytics to transform cloud infrastructures into resilient ecosystems.
Every architecture I design follows one core rule: security must move faster than risk. From IaC blueprints to real-time anomaly detection, my work blends engineering precision with strategic foresight. I'm fluent in automation, observability, and compliance engineering, and I continuously evolve systems to stay ahead of emerging threats including quantum-era risks.
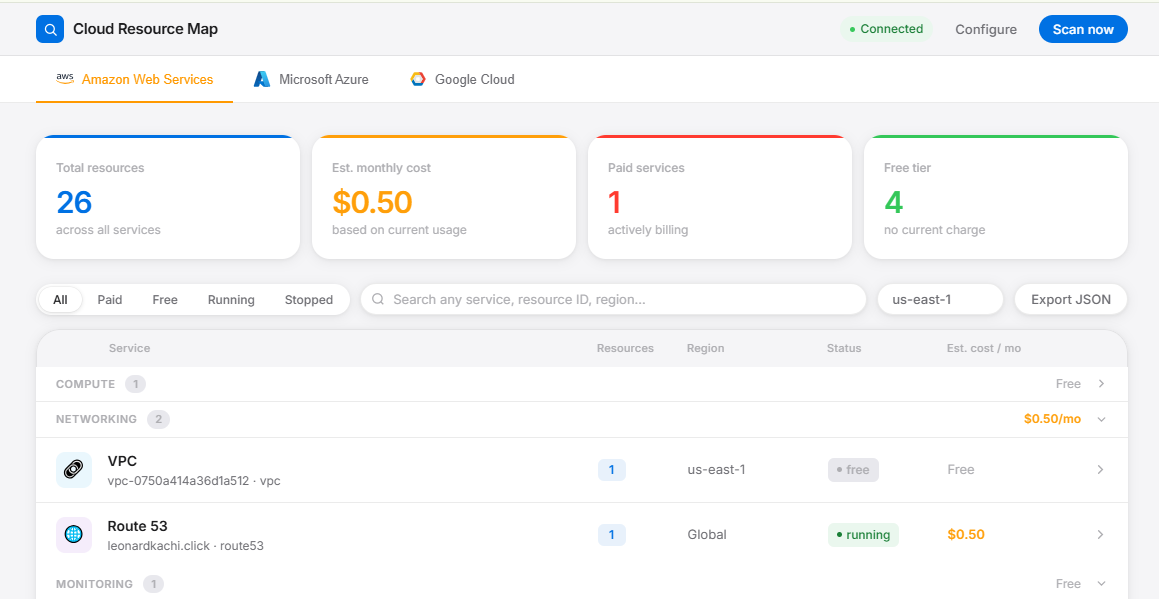
Built a Multi-cloud resource visibility tool for AWS, Azure, and GCP. to view every service running in your account or Organization Accounts, what it costs, and what region it lives in from a single dashboard. Built with FastAPI, Boto3, and Docker. Beginner friendly.

Owned a production Flask API end-to-end, containerized with Docker and Gunicorn, with a GitHub Actions CI/CD pipeline that tests and builds on every push. Deployed simultaneously to AWS and Azure with structured logging and real-time observability.

Built a machine learning model that detects anomalous behavior in cloud logs with 94% accuracy, enabling automated early warning before threats escalate into incidents.

Architected a Zero Trust security model across AWS environments, enforcing least-privilege IAM policies, SCPs, and network microsegmentation to eliminate implicit trust at every layer.

Automated CIS benchmark compliance checks across AWS accounts using Python and AWS Config, cutting manual audit time by 70% and enabling continuous compliance validation at scale.

Built a Python tool that automates security posture checks across AWS environments, surfacing IAM misconfigurations and compliance gaps before they become exploitable vulnerabilities.
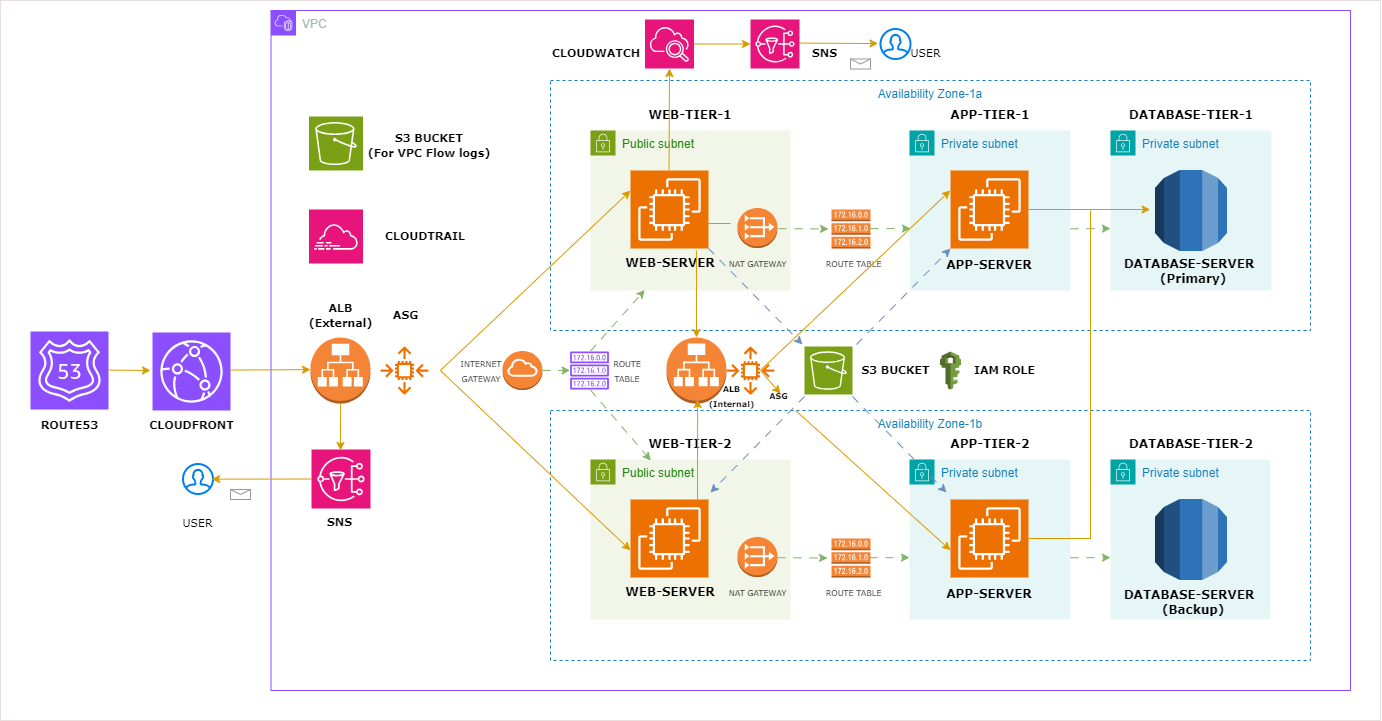
Engineered a production-grade, highly available three-tier application on AWS with VPC networking, autoscaling, load balancing, and multi-AZ database deployment built for resilience and fault tolerance.

Designing a scalable Gas discovery platform that helps drivers locate nearby stations based on real-time availability, pricing, and queue status using serverless AWS infrastructure and location APIs.

Built a serverless API for curating literary collections, leveraging AWS Lambda to interface with the Google Books Archive with keyword discovery, temporal filtering, and paginated archival responses.
Interactive demonstrations of cloud security concepts and attack simulations
Test cloud IAM policies against sample API actions to understand access control patterns and least privilege principles.
Simulate common cloud attack patterns and see how security controls can prevent them.
Explore how Zero Trust principles apply to cloud environments with this interactive demo.
Authenticate and authorize every request based on all available data points
Grant just-in-time and just-enough-access with risk-based adaptive policies
Minimize blast radius and segment access to prevent lateral movement
Real-time analysis of all network traffic and access patterns
Divide networks into secure zones with individual access controls
Implement AI-driven threat detection and automated remediation
Consistent security policies across all environments and devices
Data encryption in transit and at rest by default
Visualize security groups and network ACLs in a cloud environment.
Click on an instance to view its security group rules
Have a project in mind or want to discuss cloud security?
Reach out through the form or directly via email.